Microsoft, this is why people do not deploy NAP, NAC and other things like this, small little problems that take hours to fix – and then when something goes awry later on, people pull their hair out.
If you are running Windows 2012, with Windows 8 Desktops, everything is happy in your world.
The same is true for Windows 2008, and Windows 7 Desktops.
However as Microsoft changes things, and starts to deprecate protocols, features and functionality we keep running into cross version funnies, here is one.
A typical wireless network with 802.1X Enterprise Auth requires a few things.
- AP’s or a controller that knows where to go for authentication
- Some kind of RADIUS server that can respond to auth requests
- A certificate that is trusted by everyone involved — trusted and apparently formatted right.
The 1st and 2nd parts are pretty easy, but the 3rd, that’s where things get interesting. First it’s not totally obvious that Microsoft NPS needs a certificate, and to add insult, you need to use PEAP instead of Password Authenication — but more on that later.
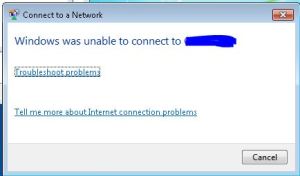
While configuring a clients Wireless for 802.1X authentication, I ran into clients who would refuse to connect, they were Windows 7 clients. Windows 8 clients, mobile devices were all fine.
Ok….. So let’s go check our event log on the NPS server…. We see Error 6273 Reason 16
Ok.. so Authentication failed due to a user credentials mismatch. Either the user name provided does not map to an existing user account or the password is incorrect. This is easy… Wait.. is it? I clicked on the network, it used my WINDOWS CREDENTIALS.. I did log on to this laptop right? Let’s do the logoff/logon dance, make sure we are wired, and we know the cred’s are right… Did that. Logon to another PC — check. Logon to a DC directly with same test account — check. Ok we know this user and password are fine.
I wish I could find something that proves why this isn’t working but I ran across this article
https://technet.microsoft.com/en-us/library/cc731363(v=ws.10).aspx
When selecting a certificate for NAP
“Certificates that do not contain a Subject name are not displayed.”
Oh, well in 2012 they are… That’s because Windows 8 clients are OK with that… Except Windows 7 clients ARE NOT.
I was also tossed the wrong way by multiple articles that claimed it was something to do with the “validate certificate” checkbox — which by the way, should be checked, why would you EVER turn off certificate validations checking! If you do that, cred’s are easily stolen by nearby attackers.
So yes, this is a bit of a ranty post, but I want to get down to this… Let’s make this work.
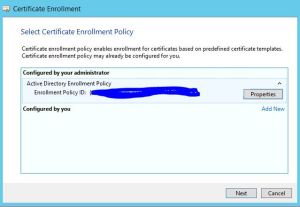
The key is when you request your machine certificate.
Start your enrollment
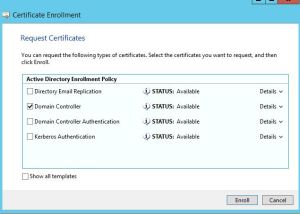
MAKE SURE YOU SELECT DOMAIN CONTROLLER — Not Authentication or Kerberos — as much as those might sound like what you want. Those certs would be published, without a subject. Click Enroll, no need to modify more
No go back and open the cert you just created… Make sure the “Subject” line has something in there, yes, the yellow bit that I have blacked out, should have the computer name in there.

Here is a good guide an example to RADIUS with NAP for Meraki. It is the same for any other wireless provider. Use this guide to finish up.
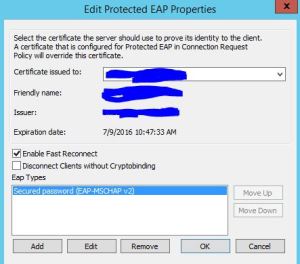
In the above guide it calls out the PEAP section, make sure you select the cert you just created.
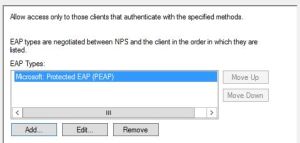
Another common mistake… In the box below you should see Protected EAP (PEAP) DO NOT ADD MSCHAPv2 “secured password” — again, it might sound like what you want, but it is not.
So that’s it, yes a little bit ranty. This needs to be easier, if I was a powershell guy, I am certain I could write a script that just does this for me, you can even add radius clients with New-NPSRadiusClient and create all the policies in PowerShell, but I am simply not a programmer.
Microsoft — this does not need to be this difficult.

Nice! This article helped me resolve a nasty authentication issue with one of my clients. Great job!
LikeLike
Thanks man you just saved me a few grey hairs. I was using a server certificate with DNS name in the SAN and no subject name, and authentication by a Windows 7 client was failing. Never would have guessed that was the problem.
LikeLike
what if I use a public wildcard certificate like DigiCert?
I am having the same error message, where I am not able to connect to the SSID with Windows 8/10. No issue with Android and IPhone.
LikeLike
Windows will not accept a wildcard cert for 802.1X
LikeLike
Dude, can I buy you a beer?
I read almost everything on the internet trying to solve this problem.
LikeLike
Thanks!!! Well if we ever cross paths, deal! Glad it’s helping so many.
LikeLike
Another beer owed! Thank you this really helped me out as well! Cheers
LikeLike
OMG. I’ve just spent 3 hours trying to figure this out. I couldn’t find anything on Google relating to this issue until I stumbled upon your article. It was working fine on my windows 10 computer, but not Win7. Thanks man you saved the day.
You don’t even have to install the certificate on the client computers like all the other articles were saying…it gets it from the server. At least…that’s what I’ve discovered so far…on to more testing!
Seriously…WTF Microsoft.
LikeLike
Just to confirm. This article is amazing. Thank you so much!
LikeLike
Thanks so much. I ran into this problem and google-fu just wasn’t working so I am glad this is helping others.
LikeLike
Thank you so much for this!
LikeLike
Awesome! You helped me alot!
I almost needed to roll back and disappoint the customer 😀
LikeLike
First of all, Thank You very much for this.
I ran in the same Problem at our Company. I tried to fix the problem with your solutions but the Thing is
i can not enroll a domain Controller Certificate because the NPS server is not a domain Controller.
then i tried a OpenSSL Certificate Web server Cert and a IIS Self Signed Certificate which also did not work out. Any Ideas?
LikeLike
Hello,
i setup NPS and CA on same virtual machine, i created local CA and setup correctly NPS.
For mobile phone or windows 8 it is working correctly, but for Win 7 i still getting message “windows was unable to connect to RADTEST”. In the events log on NPS is “The certificate chain was issued by an authority that is not trusted.”
Certificate has subject with the local hostname + domain. If i import this certificate directly to device then the connection is working. Why i dont get simple warning about that certificated is not trusted with the choice to continue?
Could you give me the advice?
LikeLike
Thank you very much, you saved my life 🙂
LikeLike
Just amazing, thank you!
LikeLike
Is anyone around still who could tell me where and how you run Certificate Enrollment? Our environment was setup by multiple vendors and we are cleaning up. Thank you.
LikeLike
Actually, I found it. You just create a new Cert on the NPS server, but we don’t have Domain Controller as an option. We have are own offline root, and subordinate CA’s on our domain. Any ideas there?
LikeLike
Thank you so much to take the time to write this article !
LikeLike
In 2020 with windows server 2016, this is still relevant. Thanks a lot for taking time to write the blog. Helped me today.
LikeLike