iOS 10 will be available on September 13th – This means that on that day your network is going to get hammered. 100 employees, even on a 1GB internet link could reek havoc into your network when they all start downloading the iOS 10 update at work.
Why at work? Limited download speeds at home, limited bandwidth at home, bored at work – whatever it is, each time a huge iOS update is announced, I get calls about slow networks. This is especially important for Guest and Public Access internet services – stadiums, ice rinks, recreation centres – or as many think of it ‘That spot I go to download!’
Protect Quality of Experience With Meraki
The last thing we need is this new Apple download getting in the way of the quality of the experience for your business apps and real users.
Meraki offers a few options for helping with this, and it is as easy as a few dashboard changes. If you are using a mixed MX/MR environment, I recommend doing this both at the wireless and at the edge, especially because desktops can pull the update as well.
Remember – Layer 3 rules are always processed before layer 7 rules so this is only a tip, you might be adding this to your existing rule set so take care. You may need to add this to group policy if you have deployed individual group policies based on VLAN or AD Group.
Capture The Right Traffic!
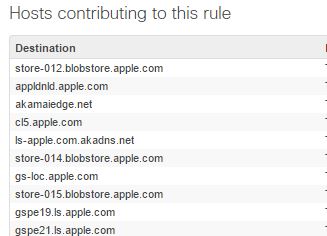
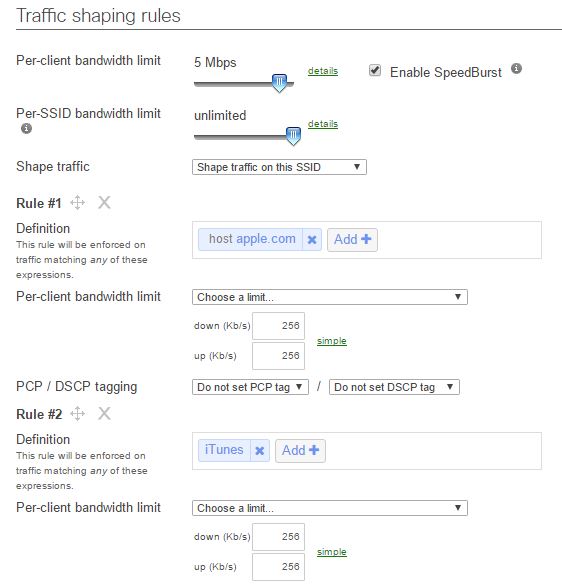
Meraki categories iTunes updates as “Music” so to throttle this properly we actually need to use the Music category, but many Apple updates also come down using an application that identifies simply as Apple.COM. So to ensure we catch this, we should create two rules to ensure that we are catching ALL of the traffic types. Technically Apple could use different methods to distribute the new update, and we do not know what they will use or how it will be categorised.
Users also have the option of downloading the update to their PC – which might technically be iTunes Traffic. We cannot look into the future, so I plan to be sure to catch this traffic by creating a few rules
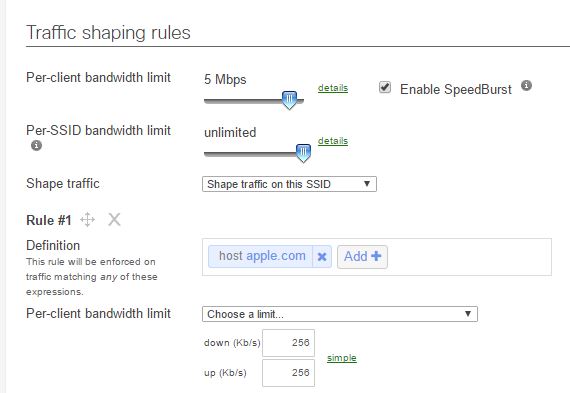
An intelligent way to do this could be to look at how many users you think you have and then throttle based on a calculated amount, if you have 100 meg internet, and 200 apple devices and want to use 50MB max, you could give 256K / user. Remember traffic shaping is per session.
These rules should be added to both the traffic shaping for your wireless, and for the MX device if you have both.
Throttle apple.com
This traffic identifies as “Application: Apple.com” so we need to create the appropriate rule.
In this case I am going to limit each user to 256K, I don’t want to totally prevent it from working – but I don’t want 100 people eating my network – 200 x 256K is 51Mb!
Throttle “Music”
Sometimes iTunes traffic identifies as Music.
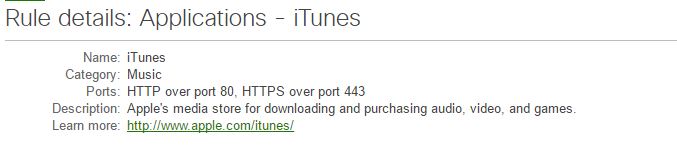
So we need to ensure we capture that traffic as well, the nature of Apple’s environment makes it difficult to figure out how they will distribute this. Once again as above, we will limit it to 256Kb
That is it! You are protected against the onslaught of Apple Update madness.
Great article – thanks!
Is there any reason why you didn’t combine these into a single rule?
LikeLike
No specific reason actually – I guess I could have combined them!
LikeLike
I did – and I guess I’ll find out today just how effective it is!
LikeLike