Meraki has been in the limelight for some time, however when Cisco started to really put money into the organisation, and let them use some of their IP, the R&D really took off. In the past year and a bit we have seen amazing things come out of the Meraki camp, and the new MC74 telephone is just one of those very interesting developments.
Many call me a “fan boy” but really I am just a “get things done” person – and when it comes to the needs of a large majority of my clients, I can get things done, faster and better much of the time with Meraki.
I really see Meraki as ahead of its time, if you look at disruptive technologies like the Apple Newton or Google Glass – these were all technologies that simply came out too early. This is why I feel many people do not understand the real benefits of something like Meraki.
Why am I calling it “Meraki” – why not talk about switches, routers, firewalls and features. That’s because just like Meraki’s own marketing campaign “Full Stack” I like to call the entire suite “Meraki” – as a single entity.
Automation At Heart
There is two camps out there right now, the SDN camp which is really focused at those doing difficult things many times – and then there is the automation camp which is really more related to doing difficult things easier.
For those in the super huge enterprise, or service provider space, they need to automate difficult things because it takes a long time. For those in Medium business space, we need to automate because it makes what we do easier, Cisco is leading the way with features like iWAN App and EasyQOS are leading the charge when it comes to enterprise automation.
However just like these products are new, and somewhat mis-understood, I think the real value of Meraki is baked right in, it is the ability to automate the difficult tasks that provides value.
If you are an organisation of 100-250 people, your IT budget is not getting big enough fast enough, and your team is not doubling as your workload is – so making things easier to manage through automation and simplification must be a focus.
Time to Value
I keep saying that I want to have a race, pick IT equipment vendor #1, and have the best expert you have build X/Y/Z network while someone does the same on Meraki. Anyone who has worked on the stack KNOWS that the Meraki will be faster.
It’s about workflow and tools. In today’s complicated world of inter-networking technologies, in order to deliver true value I need a management stack, that means products like Cisco Prime, or Wireless Engine, or APIC – any number of tools are needed to provide next-gen network management visibility and manageability. Meraki starts with all of that — done for you — it is running already. This is a HUGE time to value.
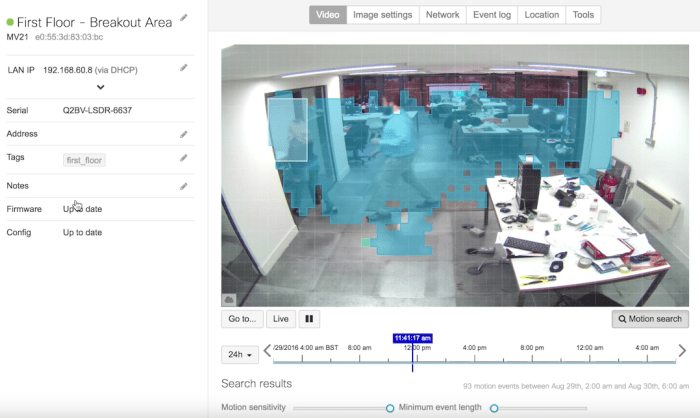
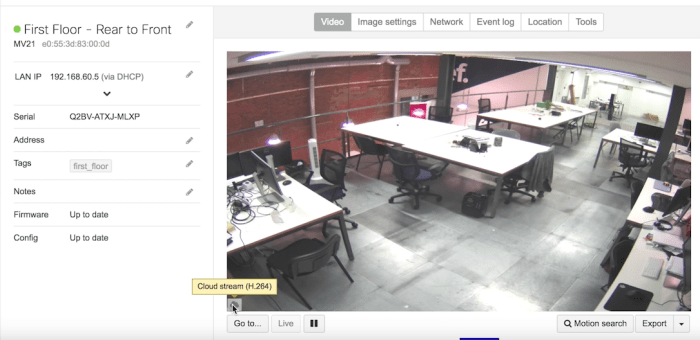
What this means is that automated, managed, monitored (all the way to Layer 7) and well operated networks are automatic with Meraki. The deployment tools, management and monitoring are where you start – not what you do when you are finished. This translates to extremely rapid time to value for customers. Add in the template capability and the fact devices are all self provisioning and you can do something that no other vendor will let you do. Program, build and deploy network equipment that is still in transit. Yes, that’s right, normally my clients networks are already configured before the hardware even hits the dock.
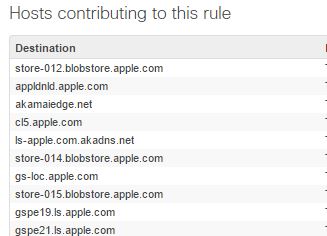
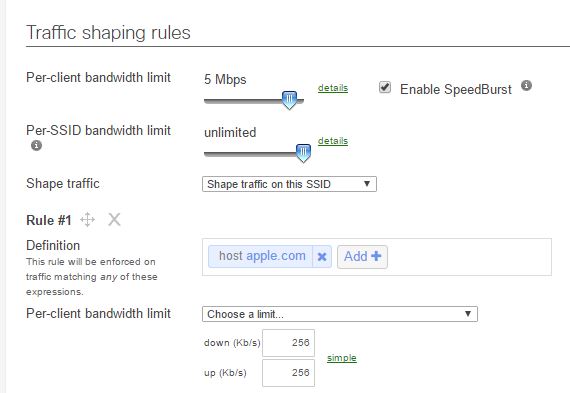
New Features – Free
When most clients purchased Meraki products last year, they didn’t get many of the features you have today, Advanced Malware Protection (AMP), iWAN, Port Isolation, templates, NetFlow, these are not small features – these are huge – and with most vendors you would be forced into a costly upgrade – upgrade, click enable on feature – done. That is one hell of a way to deliver value.
Disruptive Marketing
Why did Meraki get as popular as it did, and as a result catch Cisco’s eye? Geeks. Meraki figured out that if they can win over the geek community, they can win over the customers, after all the geeks make the product recommendations. We all knew how they did that — Free Gear — who doesn’t want some free gear to play with at home – Meraki figured out how to get geeks to try their product – fall in love with it, then buy more.
They have also started running “free switch” offers as well if you want to try those out — oh and you keep them when you are done.
This continued with their partner community. You will see partner SE’s labelled as “CMNA” Cisco Meraki Network Associate – of which yes, I am. Once you pass a test, and take training you receive this certification. Why are these classes full of students, over and over and over? — Free Lab Gear — Meraki provides a switch, firewall and AP to each person that passes the course. This also means each and every certified CMNA has their own lab to test, learn, troubleshoot and solve problems with. I have re-deployed my trial firewall at more customers as a temporary trial than I can count, every single one, ended up purchasing a Meraki MX.
Easy to Learn
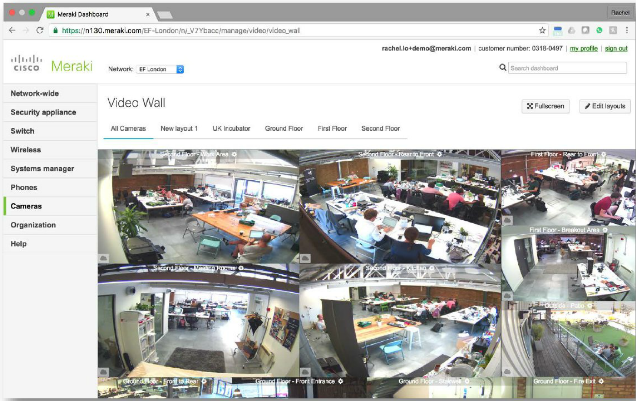
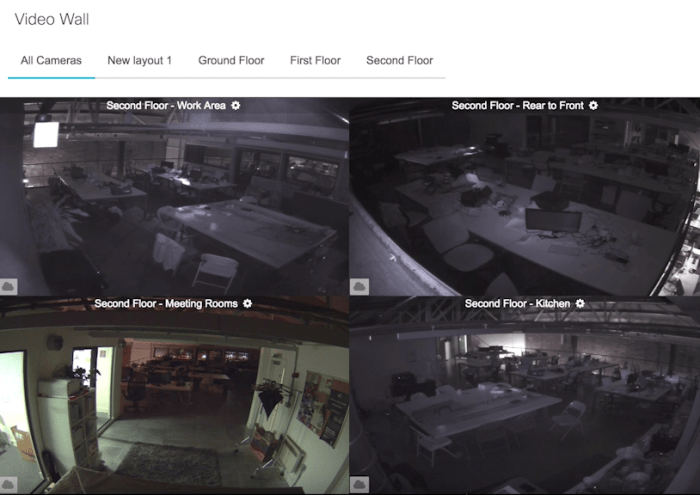
The interface is just so darn intuitive. Honestly everyone I show the interface to says things like “Wow I don’t need training for this, it is all very obvious” — and it is.
To give you an idea how obvious it is, the Meraki CMNA certification course is a single day. That is right, routing, switching and wireless – in a single day. We are not talking about expert un-boxers either, 802.1X, troubleshooting, routing protocols, firewalling, it is all covered in that single day. Caviet – they do require you to have existing skill-set, CCNA recommended.
Their training is also out of the ordinary, instead of providing you with a long list of screenshots, they identify outcomes as you build your training lab – you are not walked through how to do things – they say things like “Go to the firewall, and create a new vlan” – expecting you to figure it out. Studies have shown 80% better retention in students that figure things out vs those who are walked through something.
Subscription Fears
This is the single biggest argument I hear against Meraki. However when was the last time you purchased switches and routers from any other vendor and didn’t buy their support. Yes, I will admit there are some clients who buy switches without support and then carry spares, but that doesn’t provide you with software support, or a 24×7 helpdesk, when Meraki delivers on value, the support system really does work – with an integrated help system built right into the portal, and no fumbling around to get the vendor access to gear to help you, I swear I save at least an hour per help incident.
With security becoming a huge focus for many organisations, subscriptions can be seen everywhere these days. Luckily you get a huge amount of value from Meraki, integrated AMP and SourceFire built right in to the firewall. Customers who had purchased 3 year subscriptions, 3 years ago didn’t even have SourceFire, or AMP – but they do now. That right there is worth the cost of admission.
Summary
Cisco has left Meraki alone – and that is a good thing, the same thing happened with Linksys as well. The reality of this means the Meraki team can continue to operate as a skunk works building amazing disruptive new technologies. That does not mean that technology has not trickled down from the mothership, SourceFire, PoE power supplies, AMP and many Cisco technologies have found their way into the Meraki line up.
For clients 0-500, Meraki is a natural fit for 90% of them, but just like any product it has to be qualified, and when properly qualified for a client – no product delivers the ease of use, time to value, and overall manageability of a Meraki full stack.
I cannot wait to see what they do with that phone.